If your business technology setup is driving you nuts, you’re not alone. Many business owners and managers have endless gripes about the technology they use for their business. It could be that your Wi-Fi is crawling along and not allowing for productive Internet speeds, your software feels like it was developed for Windows Vista, or you’re constantly wondering how you are going to keep your data safe. Whatever the case, it can be fixed. In today's blog, we’ll go into how to rebuild your IT plan from scratch.
When your business’ data is so crucial to your successful operations, there are certain precautions that you simply need to take for the sake of your business’ longevity. One such precaution: data backup.
Your data is the gas that powers your business’ engine, whether you’re referring to project files and intellectual property or financial info and customer records. As such, imagine what it would mean if your business ran out of gas… or, more accurately, it was siphoned out.
Remember buying software on disks and installing it, computer by computer? Thankfully, those days are long behind us. Today, Software as a Service (SaaS) offers powerful advantages, especially for small and medium-sized businesses.
Let’s explore how you can benefit from these subscription-based tools.
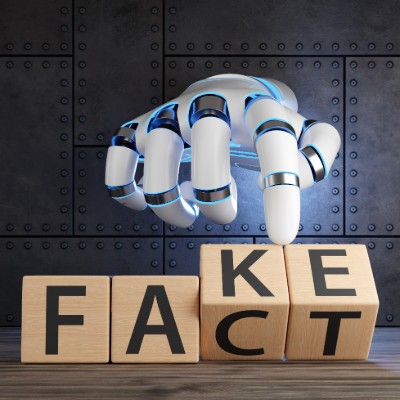
The world of cybersecurity is in constant flux, demanding that organizations continually reassess their defensive strategies. A traditional focus solely on preventing breaches, while important, is proving insufficient in the face of sophisticated and persistent threats. As highlighted in a recent Illumio podcast episode, "Trust & Resilience: The New Frontlines of Cybersecurity," the very foundation of digital interaction—trust—has ironically become a primary vulnerability exploited by attackers. This necessitates a fundamental shift in perspective.
If you're like many small and medium-sized business owners, you're juggling countless online passwords… for email, banking, software, supplier portals, and more. It's overwhelming! This often leads to using simple or repeated passwords, which unfortunately opens the door to cyber threats like data breaches, a serious risk for any business. Thankfully, there's a straightforward solution: a password manager.
Running a small or medium-sized business means juggling countless priorities. You're focused on your customers, team, and bottom line… but what about the technology that powers it all?
Often overlooked, your IT infrastructure is far more than just the computers on desks. It's the complex web of network equipment, essential software subscriptions, cloud services, and even the personal smartphones and tablets your employees use for work. Keeping this entire ecosystem running smoothly and securely is a significant challenge for many SMBs.
Small businesses today generate a lot of data. From customer details and sales records to inventory tracking and employee schedules, you need to be able to structure this data so that you can use it effectively. Keeping that data organized and accessible is important, but managing it effectively can often be a hassle. This is where smart database management comes in. When done right, it helps businesses run smoother and often save money.
It is great to have pride and confidence in your business, especially in the team you’ve assembled… including your in-house technical support team. That said, even the most capable IT team may not fully meet a business’ needs.
Let’s explore why this is and what can be done to correct any deficits your team may encounter.
Data storage can be difficult for SMBs to manage, but the cloud can make it significantly easier (and cheaper). There are real, tangible benefits of using the cloud for your data storage needs. Today, we’ll look at three major reasons why your organization should have cloud storage on its list of tech infrastructure priorities in the coming months.
Bring Your Own Device, or BYOD, is a common approach for businesses that want to take advantage of mobile technology to kickstart productivity. Instead of supplying each individual employee with company-owned devices, businesses allow employees to use their own devices for work-related purposes. While this is great on the budget, it’s only really effective (and safe) if the employee prioritizes security on their devices; otherwise, it’s a liability.
Today is World Backup Day, an annual reminder that losing your data is just one accidental delete, cyberattack, or spilled drink away. The idea is simple: back up your files before disaster strikes. Because trust me, nothing ruins your day faster than realizing all your work, memories, and important files have vanished.
We’re sure your business has at least a couple of employees who spend part of their workday in a different location, but are you doing all you can to help them be as productive as possible? While remote work is beneficial in so many circumstances, there are a lot of caveats to it that must be considered. Today, we want to go over how you can mitigate risk and keep remote work from becoming a liability for your company.
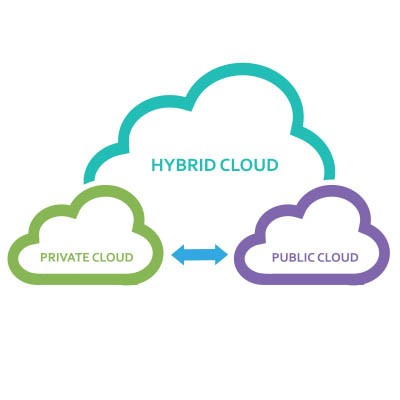
Whether you’re aware of it or not, you’re likely already utilizing the cloud in at least some capacity. The trick is to find the best way to manage your business’ cloud so that it works for your organization’s specific needs. Today, we want to look at the different types of cloud management policies and why you need to weigh your options to get the most value for your business.
It’s no secret that Google Chrome is one of the most popular web browsers in the world, if not the most popular. Still, most people don’t use the browser to its full potential, and they leave so many wasted opportunities to save time and resources on the table. Today, we want to highlight some of these tips, but also a couple of features that perhaps you didn’t know existed for Google Chrome so you can continue to get more value out of it as a business and productivity tool.
The Android operating system periodically receives updates and patches detailed in online publications called Android Security Bulletins. In the March 2025 edition, Google announced that 43 malicious bugs had been resolved, two of which were zero-day vulnerabilities.
Let’s talk about how to implement these fixes and why this is a practice that should reach every aspect of your business’ IT.
It should come as no surprise that cybersecurity is a big challenge for businesses and individuals alike. The problem: life pretty much revolves around being online these days, so there’s no avoiding it. Therefore, it’s your responsibility to ensure that any data you collect from your customers, employees, and other key stakeholders in your business is well-protected, otherwise you will face severe consequences.