The password isn’t nearly as secure as it used to be. Hackers have begun to take advantage of extremely powerful solutions designed to brute force their way into accounts by using software to rapidly guessing thousands of passwords per second, making it extraordinarily difficult to prepare yourself for them.
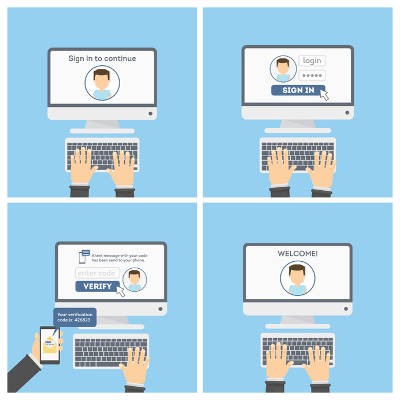
What’s the best way to guarantee that passwords aren’t going to be the downfall of your company? A great start is by taking a close look at password best practices and two-factor authentication.